During the 1990s a variety of defence forces from around the globe began to look at the impact of new technologies on combat effectiveness. For the first time the infantry man was studied as a complete combat system, with a view to enhancing his/her mobility, survivability, strike power and communications.
These programmes culminated in September 2000 with the first operational test of Land Warrior system by the American 82nd Airborne Division. The core objective of Land Warrior revolved around the application of commercial technology and its use in conjunction with existing military hardware to provide the infantry man with enhanced situation awareness. Situational awareness was deemed critical, as a more informed soldier was obviously going to be vastly more effective in any combat role.

Discover B2B Marketing That Performs
Combine business intelligence and editorial excellence to reach engaged professionals across 36 leading media platforms.
These Land Warrior systems focused on the incorporation of digital maps, intelligence information and imagery from a weapon-mounted thermal weapon sight (TWS). The visual elements of the system included a video camera, a helmet-mounted display and an M-4 carbine equipped with the TWS enhancements.
Land Warrior-equipped soldiers also benefited from and a laser rangefinder / digital compass and enhanced communications with an integral computer / radio subsystem that provided both voice and wireless data communication capabilities.
It was a comprehensive approach that proved to be very heavy when evaluated in combat (during the first Iraq war). However the system also served as a great proof-of-concept as the basic idea showed sufficient promise to justify a ‘second generation’ development of the technology.
IMPLICATIONS FOR THE BATTLEFIELD OF THE FUTURE
The introduction of these systems has immensely significant tactical implications. The integrated use of wireless communications, GPS receivers and thermal sights allows for the implementation of dispersed yet highly coordinated deployments at night or in adverse conditions.
This ability to coordinate troops with greater sophistication effectively acts as a ‘force multiplier’.
It allows a platoon or company commander to dynamically control the battle-space by providing them with real-time positional data on friendly forces, known enemy forces and the provision for the dissemination of voiceless non line-of-sight communications.
It almost makes controlling the battlefield play out somewhat like a sophisticated real-time strategy computer game, as the real-time input and force movement controls makes it possible to react, anticipate and respond as fluid battlefield dynamics change minute by minute.
Successive live fire trials of the Land Warrior system demonstrated this ability, with Land Warrior-equipped soldiers showing a clear advantage over non-equipped forces.
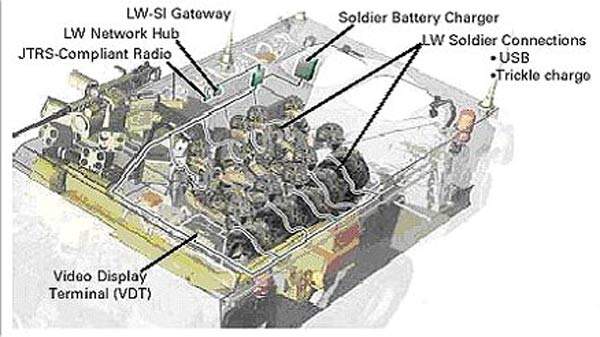
However arguably the most revolutionary aspect of the Land Warrior was the fact it helped the infantry man operate as a data collection sensor via the Land Warrior Stryker integration kit, which provides for the extension of individual soldier’s personal area network to allow voice and data communication with dismounted Land Warriors, Land Warrior units mounted in other Stryker vehicles and integration into the Army Battle Command System and Force XXI Battle Command Brigade and Below (FBCB2) Appliqué. (see images one and two on the right).
Though broadly successful, subsequent trials and a recent deployment to Iraq courtesy of the 4th Stryker Brigade Combat Team uncovered a number of shortcomings. The most significant of these is the significant time lag regarding map updating. Other issues such as high unit weight, low battery life, outdated electronics and optics also caused concern. These shortcomings combined with a continued high cost of $30,000 a unit resulted in the abandonment of Land Warrior in February 2007.
Though less than successful in its first generation, as a proof of concept the Land Warrior system demonstrated its potential to act as a force multiplier by radically altering the force projection capabilities and combat effectiveness of the infantry utilising it. Through the use of emerging commercial technologies it is becoming possible to generate effective solutions for all shortcomings identified as a part of the Land Warrior evaluation.
WORLDWIDE GROWTH
Recognition of this is best demonstrated in the number of countries establishing what can broadly be termed ‘future soldier’ programmes. These programmes include Land 125 (Australia), Félin (France), IdZ (Germany), Combatiente Futuro (Spain), Soldier Modernisation Programme (Netherlands), NORMANS (Norway), Soldado do Futuro (Portugal), IMESS (Switzerland), MARKUS (Sweden), ANOG (Israel), FIST (UK), BEST (Belgium) and Objective Force Warrior (USA).
Arguably the most ambitious of these programmes is the Objective Force Warrior (OFW) programme. Established in 2002 as a replacement for Land Warrior, OFW seeks to implement a holistic solution to equipping, monitoring and communicating with the future infantry man to produce a soldier with 20 times the effectiveness of the current soldier.
Central to the OFW programme is replacing the bulky, fragile and power-hungry systems of Land Warrior with lightweight reliable full-spectrum enhancements with much greater capabilities. These enhancements include better augmented weapon systems, individual armour protection, performance and medical aids, worn power sources, enhanced communications, sensors and modern computer systems.
Within OFW existing sensors and targeting aids have been integrated within the helmet to provide infrared, thermal, day / night video feed and chemical / biological sensor data on a visor approximating two 17in displays in front of the soldiers’ eyes.
Equipment has even been embedded in worn uniforms with the integration of physiological sensors to allow for the command / medical monitoring of life signs. These new technologies are going to make it far easier to aid troops in the field and should have an impact on casualty rates through the early detection of injuries and more efficient response to critical situations.
C4I?
In conjunction with the strategic and tactical benefits that networked infantry are set to provide the future army, the same technology presents a series of significant security challenges.
In light of the old IT adage ‘the only secure computer is one locked in a buried box’ the widespread introduction of C4I (command, control, communications, computer and intelligence) networks looks set to bring to prominence the battle for ‘electromagnetic dominance’ in future conflicts.
These systems themselves could be attacked and any attempt to impinge upon their effectiveness has to be anticipated.
With the increasing reliance on computer networks and the advantages they afford such equipped militaries, the introduction of asymmetric strategies to counter them via the use of hacking, jamming or ‘spoofing’ has become central to the strategic thinking of a number of military organisations.
Increasing indications from within both Russia and China point to a growing realisation that while true technological parity with the US may indeed not be possible the US reliance on computer networks represents its greatest vulnerability.
Additionally the dispersal of the technology to the infantry introduces a new level of vulnerability to military C4I networks. The capture of soldiers or vehicles could present a much greater issue as the enemy would then be able to try and access C4I networks and use this equipment against the force that originally deployed it. While in past conflicts any such captures provided only limited tactical information, future captures provide the potential for enemy forces to access data networks and acquire a wealth of information unthinkable only a decade ago.
Integral to the defence against both network attacks and equipment capture is the introduction of high-level network encryption and the ability of the network to isolate and exclude suspect equipment. At present the primary wireless standards utilised are centred on the IEEE 802.11 standard, with the technology used in vehicular applications, command posts, ad-hoc networking for special forces and the networking of unattended ground sensors for surveillance, force protection and intelligence
gathering.
Future applications centre on the enhancement of IEEE 802.11 capabilities not only in terms of range with current modified COTS (commercial, off-the-shelf) technology providing up to 25km² of coverage for omni-directional antenna or 30km for directional (e.g. Elbit MaXess).
But the introduction of high-level encryption to provide secures ad-hoc networking or wireless communications for both a point-to-point and point-to-multipoint connectivity.
The introduction of such measures allow for field users share voice, video and data over a secure network (e.g. SecNet 11 Plus).
However as with all new military technologies the arms race of measure, countermeasure and counter-countermeasure has only just begun.





