
Ensuring the security of military systems against cyber attacks is a double-edged sword. On the one hand, some of the most secure systems and procedures are available, but on the other they are subject to even more intensive attacks than civilian systems, and the results of hacking could endanger military operations and personnel.

Discover B2B Marketing That Performs
Combine business intelligence and editorial excellence to reach engaged professionals across 36 leading media platforms.
Cyber security expert Giles Peeters discusses the inbuilt security offered by low-orbit satellite communication and how the tactical value of data and the security level assigned to it may need to be re-evaluated, in terms of what the potential results of a spoofing attack may be.
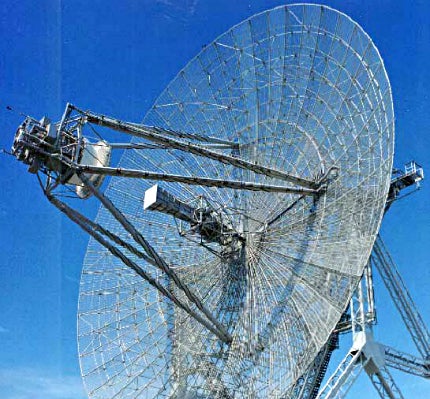
Satellite security
Giles Peeters is defence director with Track24 Defence, a group that provides situational awareness and command and control systems using commercial off-the-shelf (COTS) components to defence and government markets worldwide.
"We provide situational awareness, command and control and panic alerting using tactical data to enable commanders and managers to manage their people," says Peeters.
"Our blue-force tracking systems provide a shared picture for allied militaries to see where friendly forces are and make intelligent decisions on how to plan an operation or manoeuvre without risking friendly forces."
Track24’s systems use satellite technology with proprietary waveforms to help prevent spoofing and cyber attacks. They communicate over the low-orbit Iridium satellite constellation, which means the transmitting devices are low-power and transmit upwards rather than across the ground like radios, making them harder to intercept.
"These types of systems are valuable in this community and should be looked at more," says Peeters. "The US is using Iridium for more and more of their sensitive data; they see it as a proprietary network."
Peeters used the inherent security in satellite communications when he served in Joint Helicopter Command in Afghanistan during Herrick One, as part a group providing a tactical laydown plan for communications technology.
"We didn’t have beyond line of sight (BLOS) communications at first, and that is the biggest vulnerability in military operations," he says. "Satellite technology suddenly proves to be a viable means as it’s less susceptible to attacks."
Data significance and spoofing
One type of attack that could be particularly dangerous in a military context is spoofing, when attackers substitute false information into a situational awareness system.
"You bring this technology in and you have dots on the map that tell you where all your aircraft are," says Peeters. "We’ve got to be careful about how much we rely on that information and the decisions we take on that information if it’s vulnerable to spoofing. If you get an emergency alert from someone, do you send personnel recovery to get them immediately or verify it first?"
Peeters strongly believes that when it comes to spoofing the significance of data in different systems should be carefully evaluated for its level of military security. For example, a logistics system may be unclassified as it does not contain any operational information, but if a hacker were to spoof the system to show that no spare engines were available to repair a broken Apache helicopter, it could incorrectly be taken out of service, losing capability for a deployed force.
For Peeters, the bottom line is technology must be combined with what is known in the military context as concepts of operation to ensure security.
"System providers like us can only go a certain length," he says. "We provide proprietary networks that are difficult to get into. But it’s down to military organisations and people to implement the concepts of operation to ensure the systems are used in a secure way."
"Unkillable" malware
A secure backbone, up-to-date cyber security systems and a practical implementation plan go a long way towards ensuring military and civilian systems alike are protected from unauthorised access. But could there be a threat on the horizon that no current procedures can guard against? Part three of our special features explores the possibility of "unkillable" malware that spreads between systems, even when entirely unconnected to a network.
Related content
The enemy within – the cyber threat in every office
High-profile hacking cases dominate the headlines, but while the main aims of modern cyber cyber criminals are unchanged – stealing information and denial of services – hackers are finding new ways of bypassing security measures.
Video feature: Latest in Defence on WildCat robot and smart material for armour
This edition of Latest In Defence investigates a cat-like military robot, high-tech body armour that protects soldiers in a new way and a military project to simulate attacks against helicopters.


.gif)



